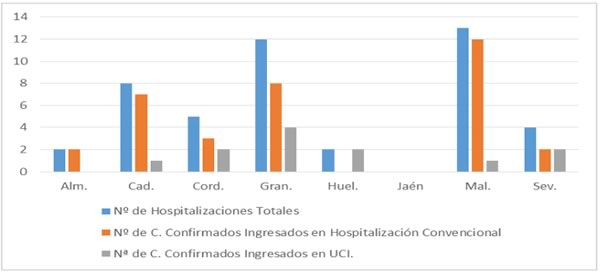
Provincia | PCR Positivo | Hospitalización | UCI | Fallecimientos | Curados |
Almería | 543 (+1) | 246 (0) | 41 (0) | 53 (0) | 744 (0) |
Cádiz | 1.316 (+2) | 593 (0) | 84 (0) | 171 (0) | 1.385 (-1) |
Córdoba | 1.353 (0) | 562 (0) | 76 (0) | 116 (0) | 1.629 (+2) |
Granada | 2.557 (+7) | 1.214 (0) | 136 (0) | 287 (+1) | 2.957 (+5) |
Huelva | 418 (0) | 223 (0) | 31 (0) | 48 (0) | 480 (0) |
Jaén | 1.488 (+2) | 778 (+1) | 91 (0) | 188 (0) | 1.730 (+1) |
Málaga | 2.959 (+10) | 1.501 (+2) | 168 (0) | 287 (0) | 3.597 (0) |
Sevilla | 2.503 (0) | 1.214 (0) | 153 (0) | 289 (0) | 2.876 (+4) |
Total | 13.137 (+22) | 6.331 (+3) | 780 (0) | 1.439 (+1) | 15.398 (+11) |
* Las pequeñas oscilaciones en el número absoluto de datos dependen de diferentes factores relacionados con la recogida de los mismos, que se realiza día a día, caso a caso, y a la mejora de la calidad de los mismos.
* El dato de positivos PCR del día anterior se puede consultar en la web del IECA.
* Estos datos corresponden a las 7:00 horas.
Todos los datos están disponibles en la web del IECA en el siguiente enlace:
http://www.juntadeandalucia.es/institutodeestadisticaycartografia/salud/COVID19.html
Actualización Brotes
Por acuerdo del Consejo Interterritorial de Salud se ha acordado considerar brotes la aparición de tres casos entrelazados o un caso aislado en una residencia de mayores. De ese modo, la actualización de hoy a las 9.00 horas es:
Provincia | Casos confirmados | Fase |
10. Málaga (Axarquía) | 7 | Investigación |
9. Granada (Metropolitano) | 9 | Control |
8. Granada (Metropolitano) | 6 | Investigación |
7. Almería (Distrito Levante-Alto Almanzora) | 4 | Control |
6. Granada (Metropolitano) | 6 | Investigación |
5. Huelva (Distrito Costa) | 10 | Control |
4. Málaga (Distrito Málaga) | 103 | Investigación |
3. Granada (Metropolitano) | 15 | Control |
2. Granada (Distrito Granada) | 27 | Control |
1. Cádiz (Campo de Gibraltar) | 25 | Control |
* Fase de control: Se ha concluido el estudio de contactos y se han realizado las pruebas según protocolos.
* Fase de superación: El brote no está activo.
* Datos provisionales en investigación.
Related word
- Near Curiosidades
- Lifestyle For Diabetes
- Curiosidades Odontologia
- Viaje Can
- Viaje 2 Actores
- Curiosidades 25 De Mayo 1810
- Viaje Tailandia
- Lifestyle Nearby
- Viaje Coche Fase 0
- Viaje Redondo
- Viaje Tnt
- Viaje 80 Dias Alrededor Mundo
- Curiosidades Estranhas
- Curiosidades 777
- Curiosidades Juego De Tronos
- Viaje 4 Dias
- Viaje 3 Dias España
- Lifestyle Xbox Games
- Viaje 1
- Curiosidades Elite
- Curiosidades Gatos
- Curiosidades Peru
- How Many Lifestyle Stores In India
- Lifestyle 180
- Curiosidades The 100
- Lifestyle Diseases
- Will Lifestyle
- For Lifestyle Meaning
- Lifestyle Wiki
- Lifestyle Publications
- Viaje Conjugation
- Curiosidades 50 Sombras De Grey
- Will Poulter Curiosidades
- Curiosidades Whatsapp
- Curiosidades Please Like Me
- Lifestyles Ultra Sensitive
- Curiosidades Y Leyendas De La Alhambra
- Viaje Travel And Tours
- Curiosidades 1917
- Why Not Lifestyle
- Lifestyle Pharmacy
- Viaje Verde Lyrics
- Curiosidades Peaky Blinders
- Viaje 2 Cast
- Lifestyle Galaxy
- Curiosidades Italia
- Viaje 6 Dias A Grecia
- Lifestyle Kitchens
- What Lifestyle Do You Want
- Is Viaje In English Word
- Curiosidades Windows 10
- Lifestyle Asia
- Curiosidades 50 Sombras De Grey Pelicula
- Curiosidades 31 Minutos
- Curiosidades Queen
- Viaje A Marte
- Lifestyle Factors
- Lifestyle Of Ias Officer
- Curiosidades Ingles
- Lifestyle Realty
- Cuota 0 Viaje Egresados
- Curiosidades 3
- With Lifestyle Meaning
- Lifestyle Markets
- Lifestyle And Wellness
- Viaje Virtual
- Viaje Y Mesa Electoral
- Viaje Kenia
- Viaje 4 Dias Pais Vasco
- Curiosidades 11 De Septiembre
- Curiosidades Libros
- Viaje Zombie Farmer Bill Hatchet
- Curiosidades Puerto Rico
- Viaje 7 Tazas
- Viaje Kenia Y Tanzania
- Lifestyle Food
- Viaje Infinito Nicole
- Curiosidades Em Ingles
- Lifestyle 45Cm Cabinets
- What Lifestyle Can I Afford
- Lifestyle Express
- Lifestyle Of A Butterfly
- Lifestyle Vs Personal Blog
- Lifestyle 76
- Curiosidades Xiaomi Redmi Note 8
- 01 Viaje Al Centro De La Tierra
- Lifestyle Without Money
- Viaje 2 La Isla Misteriosa Pelicula Completa
- Is Lifestyle An Indian Brand
- Lifestyle Centre
- Curiosidades Sobre Gatos
- Lifecycle 9500R
- What Is Viaje In Spanish
- Viaje Oro Cigar
- Lifestyle Landscaping
- Lifestyle Xl
- Are Lifestyle Condoms Durable
- Curiosidades 500 Dias Con Ella
- Viaje 1004 Kilometros Para Verte
- 4 To Viaje De Colon
- Curiosidades Xiaomi Redmi Note 8 Pro
- Curiosidades 11 De Septiembre
- Lifestyle X7400
- Lifestyle Treadmill
- Sentence With Viaje
- Lifestyle Kochi
- Viaje Farmer Bill Hatchet
- Lifestyle Asia
- Viaje Vs Viaja
- Curiosidades Interessantes
- Curiosidades Que Te Dejaran Pensando
- Curiosidades Um Maluco No Pedaço
- Viaje Guanabara
- Viaje 9 Dias Croacia
- Curiosidades De Plantas Vs Zombies Garden Warfare
- Viaje Yucatan
- Curiosidades Que Vc Nao Sabia
- Curiosidades Wwe
- Curiosidades The Circle Brasil
- Lifestyle Kuwait
- Lifestyle 360 Pearland
- When Is Lifestyle Sale Starting 2019
- Lifestyle Lite
- Lifestyle 0
- Curiosidades Nutritivas
- Curiosidades 13 Reason Why
- Lifestyle 45Cm Cabinets
- Curiosidades Nueva York
- Curiosidades 50 Sombras Liberadas
- 69 Curiosidades De Dragon Ball Super Broly
- Lifestyle Home Centre
- How Many Lifestyle Stores Are There In India
- Lifecycle 9500Hr
- Lifestyle Young Thug Lyrics
- When Will Lifestyle Sale Start
- 68 Curiosidades Sobre Israel
- Are Lifestyle Diseases Preventable
- Curiosidades Lgbt
- Curiosidades Keanu Reeves
- Viaje Travel And Tours
- Like Curiosidades
- Go Where Lifestyle
- Lifestyle 8925
- Curiosidades Windows
- When Lifestyle Is Sedentary
- Lifestyle District
- Who Lifestyle Diseases
- How Much Is Lifestyle Gym Membership
- Lifestyle Hoodie
- Viaje Que Significa
- Viaje Yellowstone
- Viaje Mitico
- Viaje 2 La Isla Misteriosa Pelicula Completa
- Viaje Oro Cigar
- Curiosidades Que Te Dejaran Pensando
- Are Lifestyle Condoms Durable
- Viaje Fantastico
- Lifestyle Solutions
- Curiosidades Friends
- Lifestyle Articles
- Lifestyle Xl Condoms Size
- Lifestyle Youtube Channel Name Ideas
- Lifestyle When Pregnant
- 007 Lifestyle
- Lifestyle Websites